We Are Stronger Charity Electronic Communications Policy
1. Purpose of Policy
We are Stronger Charity [the
The use of email, Internet and distribution list by staff, volunteers and trustees of the charity is permitted and encouraged where such use supports the goals and objectives of the Charity, however, we must ensure that communications are appropriate to the Charity's business activities and the charity is protected from risk of hacking, phishing, or legal implications arising from inappropriate use.
2. Scope of Policy
This policy applies to all staff, volunteers and trustees who are expected to always comply with the principles below.
The policy covers Microsoft 365 email communications, including the use of distribution lists, along with Microsoft Teams instant messaging, WhatsApp and Internet usage.
3. When should the charity communications facility be used?
- The Charity email address should be used for communications within the organisation, and in relation to Charity business with external persons such as donors, business partners etc... No personal email should be used for formal communications relating to Charity Business.
- Distribution lists should be used as a preferred way of communicating with a department or group as part of the charity day-to-day activities to promote business continuity.
- Microsoft Teams chat should be used for communications within the organisation that do not require information to be stored or recorded.
- WhatsApp should be used only when other channels (Microsoft 365 emails and Teams chatroom) are unsuccessful.
- No email attachments from unknown or unsigned sources should be opened in the Charity email or distribution list; Attachments are the primary source of viruses and should be treated with utmost caution.
- All employees, volunteers and trustees are required to be responsible in their use of the Internet while working with the charity and should avoid malicious websites that may put the charity at any risk.
4. Unacceptable Use
The following behaviour by an employee/volunteer is considered unacceptable:
- Use of the Charity's communications systems to set up personal businesses or send chain letters.
- Using the Charity's email and distribution list for personal communication.
- Forwarding the Charity's confidential communication (i.e. messages or email) to external email or locations.
- Distributing, disseminating, or storing images, text or materials that might be considered indecent, pornographic, obscene, or illegal.
- Distributing, disseminating, or storing images, text or materials that might be considered discriminatory, offensive, or abusive, sexist, or racist, or might be considered as harassment.
- Using the Charity's email to access copyrighted information in a way that violates the copyright.
- Breaking into the Charity's system or unauthorised use of a password/mailbox.
- Broadcasting unsolicited personal views on social, political, religious, or other non-business-related matters.
- Introducing any form of computer virus or malware into the corporate network.
- Visiting malicious or inappropriate websites while providing services to the charity.
- Downloading or storing inappropriate images, text, documents or materials from the internet to the Charity's SharePoint
5. Tone of Communication
- All communication should be polite and respectful regardless of the circumstances.
- Be aware that use of Capitalisation other than in titles can appear aggressive.
- Do not copy in anyone who does not need to know about the specific communication.
- Do not send unnecessary email - be aware that people may be suffering from email overload.
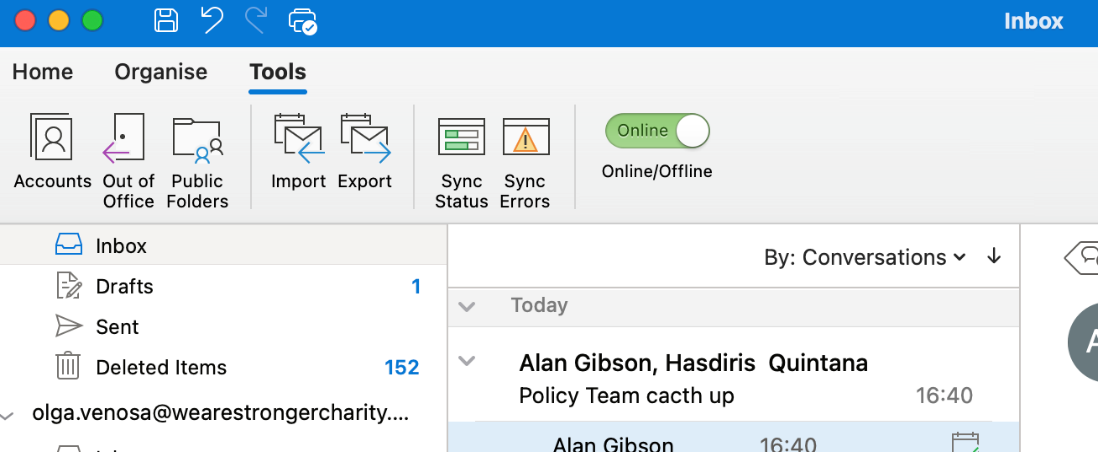
- If volunteers cannot be contacted at specific times (e.g. Holidays) then the out of office response (as shown below) should be activated.
6. Protecting the Charity from Phishing e-mails and Malicious Websites
Phishing is when attackers attempt to trick users into doing 'the wrong thing', such as clicking a bad link that will download malware or direct them to a dodgy website. Phishing can be conducted via a text message, social media, or by phone, but the term 'phishing' is mainly used to describe attacks that arrive by email.
They are likely to have a 'call-to-action.' This could be asking you to click a link or open a file, which will install a virus or some ransomware. Or it could be asking you to fill out an invoice, make a fraudulent payment, provide some personal details or log in to an account. Most of the time a savvy user will disregard these emails, as they do not come from contacts your users trust. But they can be convincing and cause real harm. Report these kinds of emails to the IT department (ITTeam@wearestrongercharity.org) of the charity without opening any attachments to the phishing email.
Malicious websites are sites that attempt to install malware on an individual's device while visiting the website (a general term for anything that will disrupt computer operation, gather personal or business information or in a worst-case scenario, gain total access to the individual's computer).
To avoid malware, all staff, volunteers and trustees are required to have active anti-virus protection on their devices at all times and update their anti-virus regularly. Details of the anti-virus will be shared with the IT Team who will monitor for compliance.
7. Monitoring of electronic communications
All of the Charity's email resources and distribution list are provided to support its vision and purpose. Therefore, the Charity maintains the right to examine any systems, email or distribution list and inspect any data recorded in them.
We are Stronger Charity reserves the right to access and disclose, for legitimate business and/or legal reasons, any message, document, or other matter sent through any communications services and equipment used by the Charity.
To ensure compliance with this policy, the Charity also reserves the right to check upon the use and content of emails and distribution list. Such monitoring is for legitimate purposes only and will be undertaken in accordance with a procedure agreed with employees and volunteers. Details of the procedure can be found in the Communication Monitoring Procedure.
Where it is believed that a volunteer has failed to comply with this policy, this will be investigated by hr_employment@wearestrongercharity.org and appropriate action taken. This may result in the requirement for further training or the termination of any volunteer agreement.
8. Review
This policy will be reviewed annually. The next review is due in June 2025.